- Audio & Multimedia
- Business
- Communications
- Desktop
- Development
- Education
- Games
- Graphics
- Home & Hobby
- Network & Internet
- Screen Savers
- Security & Privacy
- Servers
- System Utilities
- Web Development

- Softaken ZIP Recovery
- Disk Repair Utilities
- Recover USB Data Mac
- Undelete Digital Camera Photo
- Zune Files Salvage Tool
- Classroom Spy Professional
- CSV Editor Pro
- imyPass iPhone Password...
- Aiseesoft Mac Data Recovery
- AnyMP4 MP4 Converter for Mac
- Atlantis Word Processor Lite
- Quick Receipt Software for Mac
- Memory Card Data Recovery
- Allavsoft
- Files Undelete Software
- ADRC Data Recovery Tools
- avast! Antivirus
- Revo Uninstaller
- Java Runtime Environment
- AVG Anti-Virus Free Edition
- GOM Media Player
- RegSeeker
- IrfanView
- CPU-Z
- Malwarebytes Anti-Malware
- Spybot Search & Destroy
- Skype
- µTorrent
-
2Printer 5.5
Enables you to print any type documents or files in bath mode one after another specifying the paper size and without any...
-
Vivaldi for MacOS 6.6
No ad browser and uses minimum memory, takes very less time to load, some unique features added like notes containing...
-
Win PDF Editor 3.6.3
Editing PDF documents was like nightmare for me but when I am suggested by one of colleagues I tried this and found that...
-
Serial to Ethernet Connector 9.0
It can successfully turn your computer to a terminal server so that any device connected to the com port will be...
-
ShutUp10 1.4.1388
This software will let you take the full control over your windows 10 and decide which program to start automatically or...
-
TeraCopy 3.26
Copies files seamlessly from source to target location, also detects errors while transferring and rectifies it.
-
Ulysses for Windows 2.7.11
Writing application with most of useful features that a standard word processor may offer like markdown, emerging to...
-
InjuredPixels 4.0
It will repair the damaged pixels of the display unit so that it can still be usable for some more days instead of buying...
-
DrvInfo 1.2.0.2016.0
The software will show you the details of a drive as soon as it is inserted into the port whether it is a floppy, flash...
-
Unreal Commander 3.57
Can see the files in windows. You may copy, cut and paste right from there or upload to server directly.
Education / Other Education / Cryptography | Comp. Sc. Engg. 1
Cryptography | Comp. Sc. Engg. 1
Advertisement
Advertisement
Cryptography | Comp. Sc. Engg. 1 Description
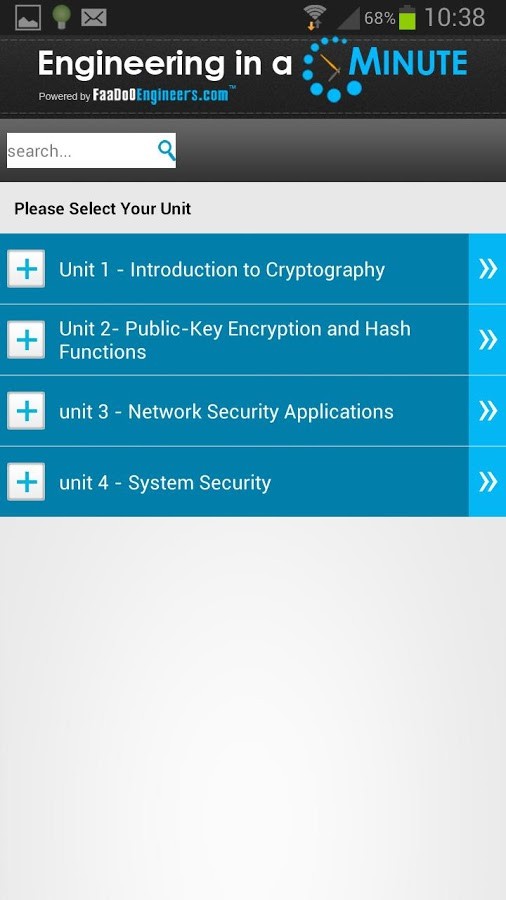
This unique application is for all students of Computer Science Engineering studying Cryptography across the world. It covers 160 topics of Cryptography in detail. These 160 topics are divided in 4 units.
This unique application is for all students of Computer Science Engineering studying Cryptography across the world. It covers 160 topics of Cryptography in detail. These 160 topics are divided in 4 units.
Each topic is around 600 words and is complete with diagrams, equations and other forms of graphical representations along with simple text explaining the concept in detail.
The USP of this application is "ultra-portability". Students can access the content on-the-go from any where they like.
Basically, each topic is like a detailed flash card and will make the lives of students simpler and easier.
Some of topics Covered in this application are:
1) Basics of Cryptography
2) Conventional cryptography
3) Key management and conventional encryption
4) Keys
5) Pretty Good Privacy
6) Digital signatures
7) Digital certificates
8) The OSI Security Architecture
9) Network Security
10) Types of attacks
11) Denial of service attack
12) Smurf Attack
13) Distributed Denial of Service Attacks
14) Security Mechanism
15) A Model for Network Security
16) Symmetric Ciphers
17) Classical SubstitutionTechniques
18) Classical Transposition Techniques
19) Rotor Machines
20) Steganography
21) Block Cipher Principles
22) The Data Encryption Standard
23) Differential Cryptanalysis Attack
24) Cipher and Reverse Cipher
25) Security of DES
26) The Strength of DES
27) Differential and Linear Cryptanalysis
28) Block Cipher Design Principles
29) Finite Fields
30) The Euclidean Algorithm
31) Finite Fields of The Form GF(p)
32) Polynomial Arithmetic
33) Finite Fields Of the Form GF(2n)
34) The AES Cipher
35) Substitute Bytes Transformation
36) Evaluation Criteria For AES
37) ShiftRows Transformation
38) AddRoundKey Transformation
39) AES Key Expansion Algorithm
40) Equivalent Inverse Cipher
41) Multiple Encryption and Triple DES
42) Triple DES with Two Keys
43) Block Cipher Modes of Operation
44) Cipher Feedback Mode
45) Output Feedback Mode
46) Counter Mode
47) Stream Ciphers
48) The RC4 Algorithm
49) Random Number Generation
50) Pseudorandom Number Generators
51) Linear Congruential Generators
52) Cryptographically Generated Random Numbers
53) Blum BlumShub Generator
54) True Random Number Generators
55) Key Hierarchy
56) Key Distribution Centre
57) Transparent Key Control Scheme
58) Controlling Key Usage
59) Confidentiality Using Symmetric Encryption
60) Link versus End-to-End Encryption
61) Key Distribution
62) Traffic Confidentiality
63) Prime Numbers
64) Fermat\\\'s and Euler\\\'s Theorems
65) Testing for Primality
66) The Chinese Remainder Theorem
67) Discrete Logarithms
68) Principles of Public-Key Cryptosystems
69) RSA Algorithm
70) Optimal Asymmetric Encryption Padding
71) Key Management
72) Distribution of Secret Keys Using Public-Key Cryptography
73) Diffie-Hellman Key Exchange
74) Example of Deffie Hellman algorithm
75) Key Exchange Protocols
76) Man in the Middle Attack
77) Elliptic Curve Arithmetic
78) Elliptic Curves over Real Numbers
79) Elliptic Curves over Zp
80) Elliptic Curve Cryptography
81) Elliptic Curve Encryption/Decryption
82) Security of Elliptic Curve Cryptography
83) Authentication Requirements
84) Authentication Functions
85) Message Authentication Codes
86) Security of Hash Functions and Macs
87) Secure Hashing Algorithm
88) Whirlpool
89) Whirlpool Hash Structure
90) Block Cipher W
91) The Nonlinear Layer SB
92) HMAC
93) CMAC
94) Digital signatures
95) Direct Digital Signature
96) Arbitrated Digital Signature
97) Authentication Protocols
98) Digital Signature Standard
99) The Digital Signature Algorithm
100) Kerberos
101) Kerberos Version 4
102) Kerberos Version 5
103) Kerberos Realms and Multiple Kerberi
104) X.509 Authentication Service
105) Obtaining a User\'s Certificate
106) Revocation of Certificates
107) Authentication Procedures
108) X.509 Version 3
109) Public-Key Infrastructure
110) Pretty Good Privacy
All topics are not listed due to character limitations imposed by Google Play Store.
OS: Android, Mobile
User Reviews of Cryptography | Comp. Sc. Engg.
-
Analog Electronic Circuits 1 This unique application is for all students across the world. It covers 147 topics of Analog Electronic Circuits in detail. These 147 topics are divided in 6 units... Download
-
Design & Analysis of Algorithm This unique application is for all students of Design & Analysis of Algorithms across the world. It covers 144 topics of Design & Analysis of Algorithms in detail. These 144 topics are divided in 5 units... Download
-
Manufacturing Science - 2 1 This unique application is for all students across the world. It covers 162 topics of Manufacturing Science II in detail. These 162 topics are divided in 5 units... Download
-
Material Science 1 This unique application is for all students across the world. It covers 143 topics of Material Science in detail. These 143 topics are divided in 3 units... Download
-
Maths for Engineers - 2 1 This unique application is for all students across the world. It covers 70 topics of Maths 2 in detail. These 70 topics are divided in 5 units... Download
-
Maths for Engineers - 3 1 This unique application is for all students across the world. It covers 76 topics of Mathematics for Engineers in detail. These 76 topics are divided in 5 units... Download
-
Advanced Database Management 1 This unique application is for all students of Advanced Database Management across the world. It covers 133 topics of Advanced Database Management in detail. These 133 topics are divided in 10 units... Download
-
Internal Combustion Engine 1 This unique application is for all students across the world. It covers 119 topics of Internal Combustion Engine in detail. These 119 topics are divided in 4 units... Download
-
Internet Fundamentals 1 This unique application is for all students across the world. It covers 100 topics of Internet Fundamentals in detail. These 100 topics are divided in 4 units... Download
-
Machine Design - 1 This unique application is for all students across the world. It covers 149 topics of Machine Design I in detail. These 149 topics are divided in 4 units... Download