- Audio & Multimedia
- Business
- Communications
- Desktop
- Development
- Education
- Games
- Graphics
- Home & Hobby
- Network & Internet
- Screen Savers
- Security & Privacy
- Servers
- System Utilities
- Web Development

- AnyMP4 Video Converter for Mac
- SSuite NetSurfer Browser
- Datarecovery Mac
- Apeaksoft Blu-ray Player
- Best Data Recovery
- AnyRec Blu-ray Player for Mac
- Aiseesoft Mac FoneTrans
- Clyton
- MindOnMap
- 4Easysoft Blu-ray Player
- EasyBilling Invoicing...
- FoneLab Data Retriever
- Informachine File Manager
- Migrate Access Database to...
- Disk Media Recovery Software
- ADRC Data Recovery Tools
- avast! Antivirus
- Revo Uninstaller
- Java Runtime Environment
- AVG Anti-Virus Free Edition
- GOM Media Player
- RegSeeker
- IrfanView
- CPU-Z
- Malwarebytes Anti-Malware
- Spybot Search & Destroy
- Skype
- µTorrent
-
2Printer 5.5
Enables you to print any type documents or files in bath mode one after another specifying the paper size and without any...
-
Vivaldi for MacOS 6.6
No ad browser and uses minimum memory, takes very less time to load, some unique features added like notes containing...
-
Win PDF Editor 3.6.3
Editing PDF documents was like nightmare for me but when I am suggested by one of colleagues I tried this and found that...
-
Serial to Ethernet Connector 9.0
It can successfully turn your computer to a terminal server so that any device connected to the com port will be...
-
ShutUp10 1.4.1388
This software will let you take the full control over your windows 10 and decide which program to start automatically or...
-
TeraCopy 3.26
Copies files seamlessly from source to target location, also detects errors while transferring and rectifies it.
-
Ulysses for Windows 2.7.11
Writing application with most of useful features that a standard word processor may offer like markdown, emerging to...
-
InjuredPixels 4.0
It will repair the damaged pixels of the display unit so that it can still be usable for some more days instead of buying...
-
DrvInfo 1.2.0.2016.0
The software will show you the details of a drive as soon as it is inserted into the port whether it is a floppy, flash...
-
Unreal Commander 3.57
Can see the files in windows. You may copy, cut and paste right from there or upload to server directly.
Network & Internet / Remote Computing / Proxy Pro 8 .10
Proxy Pro 8 .10
Advertisement
Advertisement
Proxy Pro 8 .10 Description
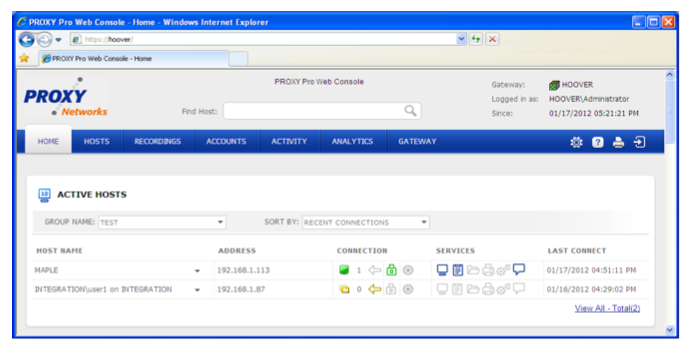
PROXY Pro 8.10 provides the software platform and tools to enable enterprises and other large organizations to host and operate their own, on-demand, web-based, in-house remote support service.
Proxy's new Pro 8.10 remote access software allows for remote access of computers, ensuring the safety and security of your computer. Customers can control the remote support service of their computers without having to worry about hazardous connections and assistance. With remote access, a properly authorized technician is given access to your PC to fix any glitches that come your way. The best part? You don't even need to be at your computer. Always-on service means that your computer can be accessed while it is unattended as well as attended, without disturbing the user. The software can also be used for the control of computers. Brand new connection management allows for the creation of a centralized directory of machines, making the control of a plethora of computers easy. Pro-8 will automatically assign or reassign Hosts to groups - without inconveniencing clients by using firewall-friendly authorization connections. Hosts can choose between audio and visual notifications to alert the user of the host's connection, which is always secure. Remote access software also provides reliable authentication measures including End-to-End, Shared-Secret, Centralized SSL, and Windows authentication for file transfers, remote access, and credential-only access. Centralized Authorization methods have been made even better, fine-graining permissions for control over a group of machines, giving chosen users different levels of authorization based upon roles and restricting access to remote machines at the customer's discrepancy. Stealth mode access can be enabled for remote machines by turning off notifications, ensuring easy auditing by a user. Additional features, such as state-of-the-art encryption algorithms and key strength, can easily be managed under a centralized audit log for easy, web-based monitoring and access. Proxy's remote access software is a way to ensure the safety and security of your computers through a trusted software provider.
System Requirements: Minimum system requirements